No. There’s no need to export the IOS-Config, deploy another Router-VM using an OVA and import the old IOS-Config to this new router.
- even, if finetuned… This strategy might lower the downtime!?
- VMware uses this strategy when upgrading NSX-Edge-Gateways very successfully!
But this is a lab environment, i’ll have to upgrade almost ten CSR1000v-Routers and there’s no time to do it manually router-by-router.
The common process is as it has been for the last decades:
- copy the new csr1000v-bin-File into the routers bootflash
- verify the file
- set the boot-variable
- reboot
Upload BIN-File into the routers
There might be dozens of valid possibilities to get the bin-file into the router.
I prefer SCP (Secure Copy Protocol) since i uses the same firewall-rules as SSH so it’s unlikely that firewalls will disturb the update process.
- i downloaded the bin-file using a windows-machine
- i’ll use PSCP from the Putty-software-suite
Basics: Loop over a set of IPs in Windows Command-Shell?
That’s all:
C:> for %i in (235,241,240,239,236,237,238,242,243) do @echo %i 235 241 240 239 236 237 238 242 243
Let’s go
c:\Users\admin\Downloads>dir *.bin
Verzeichnis von c:\Users\admin\Downloads
16.12.2017 17:44 365.660.728 csr1000v-universalk9.16.03.05.SPA.bin
1 Datei(en), 365.660.728 Bytes
0 Verzeichnis(se), 73.892.016.128 Bytes frei
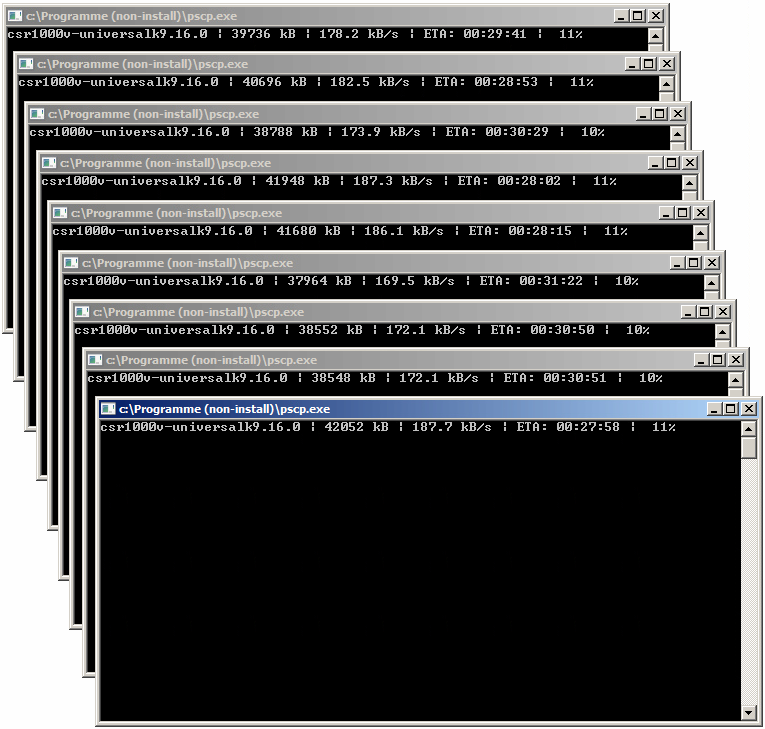
c:\Users\admin\Downloads>for %i in (235,241,240,239,236,237,238,242,243) do @start pscp -2 -scp -l rmond -pw rmondpass csr1000v-universalk916.03.05.SPA.bin 192.168.2.%i:bootflash:csr1000v-universalk9.16.03.05.SPA.bin
This will initiate 9 parallel SCP-Filetransfers:
- nobody said, this would improve the transfer speed 😉
- i’ll do something else in the meantime
Verify the transferred images
import napalm
from easysnmp import Session
#credentials
DEVICE="192.168.2.235"
USER="rmond"
PASS="rmondpass"
SNMPRW="WRITE"
IOSFILE="bootflash:csr1000v-universalk9.16.03.05.SPA.bin"
IOSMD5="49922f08698284312379b4e0a2534bc2"
VERIFIED="Verified"
SNMPOIDReload="1.3.6.1.4.1.9.2.9.9.0"
SNMPOIDReloadVal=2
#instanciate NAPALM
iosdriver = napalm.get_network_driver('ios')
#connect to device
router = iosdriver(hostname=DEVICE, username=USER, password=PASS, optional_args={'port': 22, 'dest_file_system': 'bootflash:'})
router.open()
#construct command to verify the integrity
cliVerify=["verify /md5 "+IOSFILE+" "+IOSMD5]
result=router.cli(cliVerify)[cliVerify[0]]
Set the Bootvar and check, if it’s set
#%Error verifying
#Verified
if (result.find(VERIFIED)>-1):
print "(1) uploaded File: OK"
cmdBootSystem="boot system flash bootflash:csr1000v-universalk9.16.03.05.SPA.bin"
#push boot-system-command to router
router.load_merge_candidate(config=cmdBootSystem)
router.commit_config()
cliShowBootvar=["show bootvar"]
result=router.cli(cliShowBootvar)[cliShowBootvar[0]]
#disconnet
router.close()
if (result.find("BOOT variable = "+IOSFILE)>-1):
print "(2) boot-Variable set"
print "=> Router "+DEVICE+" ready to reload"
Reload the Router using SNMP
#snmp-server system-shutdown = 1.3.6.1.4.1.9.2.9.9.0 => Value 2 => Reload
session = Session(hostname=DEVICE, community=SNMPRW, version=2)
session.set(SNMPOIDReload,SNMPOIDReloadVal,"INTEGER")
else:
#disconnet
router.close()
The Router reboots
*** *** --- SHUTDOWN in 0:00:00 --- *** Message from network to all terminals: *** Null Message
Be patient.
W-DCFW#show ver | inc IOS.*Version Cisco IOS XE Software, Version 16.03.05 Cisco IOS Software [Denali], CSR1000V Software (X86_64_LINUX_IOSD-UNIVERSALK9-M), Version 16.3.5, RELEASE SOFTWARE (fc1)
The new software-release is up and running.