The „refreshenv“-CMD/Powershell-Command updates all Environment-Variables e.g. after installing a new software package.
C:\WINDOWS\system32>refreshenv
Refreshing environment variables from registry for cmd.exe. Please wait...Finished..
networking, computing, virtualization, automation
The „refreshenv“-CMD/Powershell-Command updates all Environment-Variables e.g. after installing a new software package.
C:\WINDOWS\system32>refreshenv
Refreshing environment variables from registry for cmd.exe. Please wait...Finished..
Both Protocols are absolutely useless for all common use-cases, but enabled – just „providing“ potential security issues.
Disable like this:
netsh interface isatap set state disabled
netsh interface teredo set state disabled
I prefer accessing VMs using SSH or RDP directly. Sometimes, the IP-Address of the VM isn’t reachable, or protocols for remoteaccess need to be disabled for security reasons.
In these cases, if an IP-connection to the ESXi-Server is available this could be an option to use the ESXi hypervisor as VNC-Server to provide access to VM keyboard, video, mouse…
Three VM advanced Configuration Parameters need to be set:
RemoteDisplay.vnc.enabled = TRUE
RemoteDisplay.vnc.port = <TCP-Port>
RemoteDisplay.vnc.password = <Passwort>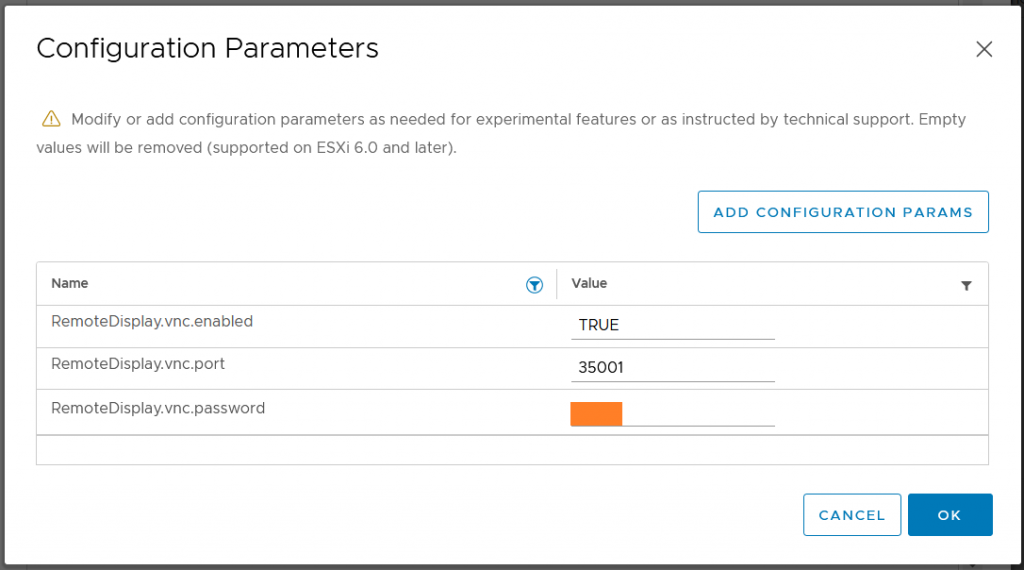
This is not for general usage, but an „admin-Jumphost“-computer/vm which needs to get flash enabled from time to time and is never used for public internet browsing…
There it might be an un-dogmatic solution to install the last Firefox 78.15 ESR Release.
Find it here: https://ftp.mozilla.org/pub/firefox/releases/78.15.0esr/win64/de/
That’s easy
That’s harder – Firefox guys (think to) know better what’s good for their users and they don’t even provide an „about:config“-switch: fail!
Add the following registry Key:
HKEY_LOCAL_MACHINE\Software\Policies\Mozilla\FirefoxAdd the following 32-Bit DWORD
DisableAppUpdatewith value set to
1and restart Firefox.
No „do you really want to leave“ windows any more, how nice is that!?
https://romanisthere.github.io
Don’t delete the content of „c:\windows\ccmcache\“ manually with the File-Explorer:
You need „local Administrator“ access to your computer.
Let SCCM to cleanup it’s cache for you:
1) open the „Control Panel“
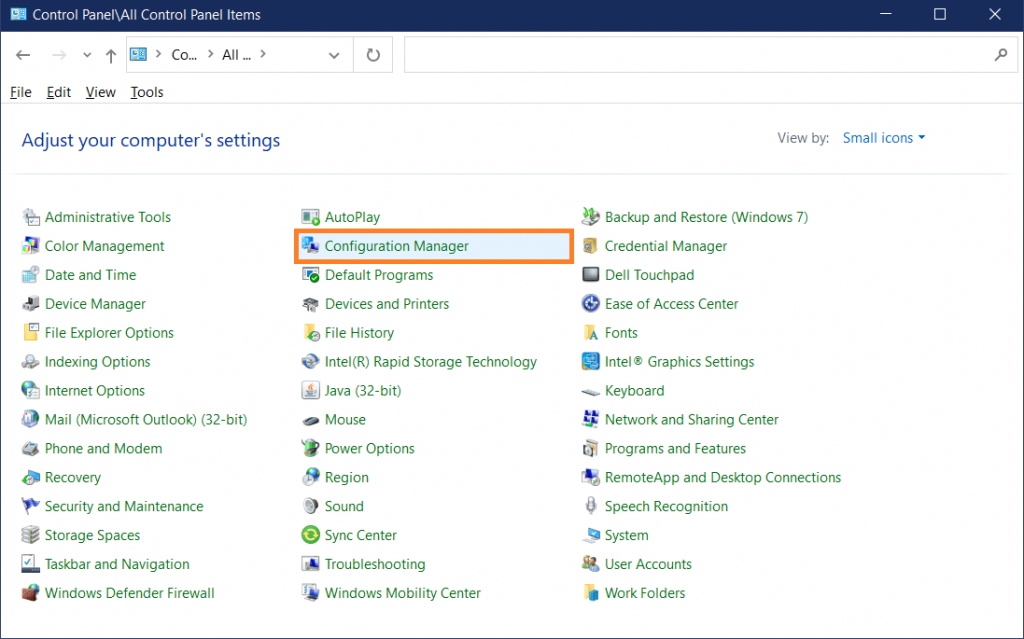
2) select „Configuration Manager“
3) go to „Cache“-Tab
4) click „Delete Files“
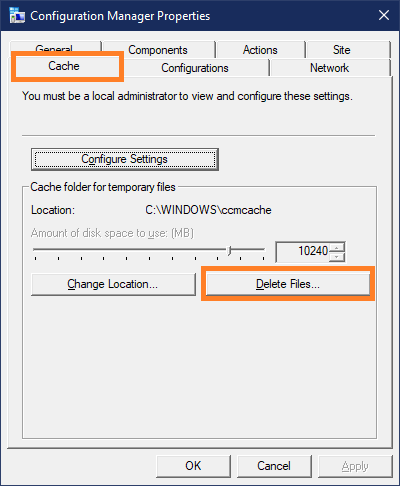
Wait a second and the CCM-Cache is empty.
c:\Windows\ccmcache>dir
Volume in drive C is Windows
Volume Serial Number is 5Q4C-0K08
Directory of c:\Windows\ccmcache
23.09.2021 19:10 <DIR> .
23.09.2021 19:10 <DIR> ..
0 File(s) 0 bytes
2 Dir(s) 11.164.721.152 bytes free
It’s a two step process to get rid of insecure username/password-authentication.
btw. Cisco-IOS doesn’t support DSA-keys
This user-account could get privileges from a Radius/TACACS+-Server which could provide access-logs, too.
I prefer Putty, usually in form of „mRemoteNG“, so i use PuttyGen to generate the RSA keypair.
C:>dir labuser*.* -l -rw-rw-rw- 1 user group 2710 Oct 17 18:26 labuser.ppk -rw-rw-rw- 1 user group 820 Oct 17 18:26 labuser.pub
C:>cat labuser.pub ---- BEGIN SSH2 PUBLIC KEY ---- Comment: "labuser" AAAAB3NzaC1yc2EAAAABJQAAAgEAg+0v9spZ0ZaBmgK3eVWJmY1Q4bNYcuY/uZDn c0JFPXgn9dA5r44GksqIEpYjkbMZf61Nkwazz4Cfxw4byS/HeajYP8Rs/eWXV6dh k829tqvqSLN6TwH+v49MllGpiHbiVGyoRvzfPgUVddN1j8cMEIJHgVJk4AS4fJmx Mp+2wMFWGldJ5xlUaOXO+XaOaTlAFYimgdYNbO7x4+vMRtrqp3ORJJZ5Tdf0JuFp cUHRlV46e2FL1FZ8p2PDLVUiAlg8o8yxI8D52r0A5VQToKz3wKUchTWIWqRmIfOR fS5jJz8+yTb/swkFs4FzAEpxD8CgvArz7ewTkna0zm8/wbysZCH1lKyce7AmZCp9 lm1Nsythl+6ztB9M01AbzBo2ElVo3GZHEr3AclsON8aCKgf8hVaZww5BqN1YHvUj dKH0Mb8i0zLs+XFSgV7rYXg1EcHyBqsRFAi5OdkuGwd5D2NfWkcwk2XBsi6qG8bP 951MlHi0SuiMTSTmskdf1OyzzIFaPYjaW9VQe36tg07MsBP48KOPEB4803k35gWx Sw2nxAO4O9KisYNCfw0SHna9RiAWRsyykLUTe6Z39vzppTEiC+j2f6IQs9Celk4S s9r8IIoI0yswtvc/DsJBLd8y0CmNwyZof9L5MSY1RlcBiCykUPh1Z+UFLEYrFBa1 qQCAwU8= ---- END SSH2 PUBLIC KEY ----
C:>egrep "^[a-zA-Z0-9+\/=]+$" labuser.pub AAAAB3NzaC1yc2EAAAABJQAAAgEAg+0v9spZ0ZaBmgK3eVWJmY1Q4bNYcuY/uZDn c0JFPXgn9dA5r44GksqIEpYjkbMZf61Nkwazz4Cfxw4byS/HeajYP8Rs/eWXV6dh k829tqvqSLN6TwH+v49MllGpiHbiVGyoRvzfPgUVddN1j8cMEIJHgVJk4AS4fJmx Mp+2wMFWGldJ5xlUaOXO+XaOaTlAFYimgdYNbO7x4+vMRtrqp3ORJJZ5Tdf0JuFp cUHRlV46e2FL1FZ8p2PDLVUiAlg8o8yxI8D52r0A5VQToKz3wKUchTWIWqRmIfOR fS5jJz8+yTb/swkFs4FzAEpxD8CgvArz7ewTkna0zm8/wbysZCH1lKyce7AmZCp9 lm1Nsythl+6ztB9M01AbzBo2ElVo3GZHEr3AclsON8aCKgf8hVaZww5BqN1YHvUj dKH0Mb8i0zLs+XFSgV7rYXg1EcHyBqsRFAi5OdkuGwd5D2NfWkcwk2XBsi6qG8bP 951MlHi0SuiMTSTmskdf1OyzzIFaPYjaW9VQe36tg07MsBP48KOPEB4803k35gWx Sw2nxAO4O9KisYNCfw0SHna9RiAWRsyykLUTe6Z39vzppTEiC+j2f6IQs9Celk4S s9r8IIoI0yswtvc/DsJBLd8y0CmNwyZof9L5MSY1RlcBiCykUPh1Z+UFLEYrFBa1 qQCAwU8=
$ cd ~/.ssh/ $ ls -l total 20 -rw------- 1 administrator administrator 1675 Aug 28 09:43 id_rsa -rw-r--r-- 1 administrator administrator 405 Aug 28 09:43 id_rsa.pub -rw-r--r-- 1 administrator administrator 222 Aug 28 11:07 known_hosts
$ cat id_rsa.pub ssh-rsa AAAAB3NzaC1yc2EAAAADAQABAAABAQCohMsS3gJ/OcF4Hg43mKeVHKWl2lECCn0iZQu9QSrUjAb4PVHWXIbj11yy5Jh/ygMys0n9IED6357fkRmq8Cc8ujpU0sCen7kBFUt3UqbLg1PLT9wMmJAEv4dcxbX9WRvwYXjLd8+EgDYDmrj7vTB3xIvw1I2WWuUK2jPWbVI57vbyGtw224Qb9Qk0KQfyGiTvErZnddDg65/rn9Pyt7FQlzCwUPH0nyJVoFhiYYJYJszTKc8BTFB6VdIbALHc4atFmjYt7YDUvEvaZqOL+zwQtr7FmXsZ5oaRGV6ZChuBPTpNEL41w/Il1mSJicRykpD90O2AxlUFebQfABTWadnr administrator@lx-ubuntu
The RFC states that the key should get split into multiple lines containing max. 72 characters.
$ cut -d " " -f 2 id_rsa.pub AAAAB3NzaC1yc2EAAAADAQABAAABAQCohMsS3gJ/OcF4Hg43mKeVHKWl2lECCn0iZQu9QSrUjAb4PVHWXIbj11yy5Jh/ygMys0n9IED6357fkRmq8Cc8ujpU0sCen7kBFUt3UqbLg1PLT9wMmJAEv4dcxbX9WRvwYXjLd8+EgDYDmrj7vTB3xIvw1I2WWuUK2jPWbVI57vbyGtw224Qb9Qk0KQfyGiTvErZnddDg65/rn9Pyt7FQlzCwUPH0nyJVoFhiYYJYJszTKc8BTFB6VdIbALHc4atFmjYt7YDUvEvaZqOL+zwQtr7FmXsZ5oaRGV6ZChuBPTpNEL41w/Il1mSJicRykpD90O2AxlUFebQfABTWadnr $ cut -d " " -f 2 id_rsa.pub | fold -b -w 72 AAAAB3NzaC1yc2EAAAADAQABAAABAQCohMsS3gJ/OcF4Hg43mKeVHKWl2lECCn0iZQu9QSrU jAb4PVHWXIbj11yy5Jh/ygMys0n9IED6357fkRmq8Cc8ujpU0sCen7kBFUt3UqbLg1PLT9wM mJAEv4dcxbX9WRvwYXjLd8+EgDYDmrj7vTB3xIvw1I2WWuUK2jPWbVI57vbyGtw224Qb9Qk0 KQfyGiTvErZnddDg65/rn9Pyt7FQlzCwUPH0nyJVoFhiYYJYJszTKc8BTFB6VdIbALHc4atF mjYt7YDUvEvaZqOL+zwQtr7FmXsZ5oaRGV6ZChuBPTpNEL41w/Il1mSJicRykpD90O2AxlUF ebQfABTWadnr
$ ssh-keygen -t rsa -b 4096 Generating public/private rsa key pair. Enter file in which to save the key (/home/administrator/.ssh/id_rsa): newid_rsa Enter passphrase (empty for no passphrase): ***** Enter same passphrase again: ***** Your identification has been saved in newid_rsa. Your public key has been saved in newid_rsa.pub. The key fingerprint is: SHA256:4g/JkvpFQmlTaOE2VQAZ9IHfz/+6NJiI8W/WVt9TJGA administrator@lx-ubuntu The key's randomart image is: +---[RSA 4096]----+ | .=B=o. | | .== . E | | .O... . . | | + o. . . .| | . + So o | | * * .oo . .| | o B o ooo. .o| | . o o .o.+. .o| | ... .o..o+. .| +----[SHA256]-----+ $ ls -l total 36 ... -rw------- 1 administrator administrator 3326 Oct 18 07:19 newid_rsa -rw-r--r-- 1 administrator administrator 749 Oct 18 07:19 newid_rsa.pub
conf t ip ssh pubkey-chain username labuser key-string AAAAB3NzaC1yc2EAAAABJQAAAgEAg+0v9spZ0ZaBmgK3eVWJmY1Q4bNYcuY/uZDn c0JFPXgn9dA5r44GksqIEpYjkbMZf61Nkwazz4Cfxw4byS/HeajYP8Rs/eWXV6dh k829tqvqSLN6TwH+v49MllGpiHbiVGyoRvzfPgUVddN1j8cMEIJHgVJk4AS4fJmx Mp+2wMFWGldJ5xlUaOXO+XaOaTlAFYimgdYNbO7x4+vMRtrqp3ORJJZ5Tdf0JuFp cUHRlV46e2FL1FZ8p2PDLVUiAlg8o8yxI8D52r0A5VQToKz3wKUchTWIWqRmIfOR fS5jJz8+yTb/swkFs4FzAEpxD8CgvArz7ewTkna0zm8/wbysZCH1lKyce7AmZCp9 lm1Nsythl+6ztB9M01AbzBo2ElVo3GZHEr3AclsON8aCKgf8hVaZww5BqN1YHvUj dKH0Mb8i0zLs+XFSgV7rYXg1EcHyBqsRFAi5OdkuGwd5D2NfWkcwk2XBsi6qG8bP 951MlHi0SuiMTSTmskdf1OyzzIFaPYjaW9VQe36tg07MsBP48KOPEB4803k35gWx Sw2nxAO4O9KisYNCfw0SHna9RiAWRsyykLUTe6Z39vzppTEiC+j2f6IQs9Celk4S s9r8IIoI0yswtvc/DsJBLd8y0CmNwyZof9L5MSY1RlcBiCykUPh1Z+UFLEYrFBa1 qQCAwU8= exit username labuser key-string AAAAB3NzaC1yc2EAAAADAQABAAABAQCohMsS3gJ/OcF4Hg43mKeVHKWl2lECCn0iZQu9QSrU jAb4PVHWXIbj11yy5Jh/ygMys0n9IED6357fkRmq8Cc8ujpU0sCen7kBFUt3UqbLg1PLT9wM mJAEv4dcxbX9WRvwYXjLd8+EgDYDmrj7vTB3xIvw1I2WWuUK2jPWbVI57vbyGtw224Qb9Qk0 KQfyGiTvErZnddDg65/rn9Pyt7FQlzCwUPH0nyJVoFhiYYJYJszTKc8BTFB6VdIbALHc4atF mjYt7YDUvEvaZqOL+zwQtr7FmXsZ5oaRGV6ZChuBPTpNEL41w/Il1mSJicRykpD90O2AxlUF ebQfABTWadnr exit exit exit end
VBOX-CSR-1#show run | section key-chain ip ssh pubkey-chain username labuser key-hash ssh-rsa CE7178C1D6D025F7EA5345CCBA22ED54 key-hash ssh-rsa ABBF42AB330CA79B235FB369FCC4D53E
ssh-rsa 4096 ce:71:78:c1:d6:d0:25:f7:ea:53:45:cc:ba:22:ed:54
so you could save time to just configure the hash.
$ who administrator pts/0 Oct 18 17:37 (192.168.56.1)
Linux re-uses the name of the current linux-user to login into the ssh-device unless a user is specified
$ ssh 192.168.56.102 Password:
The IOS-Router prompts for a password for users who have no known-public-key in the running-config – and there is no public-key for a user named „administrator“.
(config)# ip ssh server algorithm authentication publickey keyboard password
conf t ip ssh server algorithm authentication publickey end
$ ssh 192.168.56.102 administrator@192.168.56.102: Permission denied (publickey).
$ ssh -l labuser 192.168.56.102
VBOX-CSR-1>who
Line User Host(s) Idle Location
0 con 0 idle 00:02:43
* 1 vty 0 labuser idle 00:00:00 192.168.56.101
VBOX-CSR-1>enable % No password set
conf t username labuser privilege 15 end
$ ssh -l labuser 192.168.56.102
VBOX-CSR-1#who
Line User Host(s) Idle Location
0 con 0 idle 00:00:10
* 1 vty 0 labuser idle 00:00:00 192.168.56.101
Interface User Mode Idle Peer Address
VBOX-CSR-1#show priv
Current privilege level is 15
[btw. the linux-ssh-client „labuser“ is still logged in]
That’s all.
Security is important.
But sometimes it’s important, too, to be productive, for example during work hours.
Maybe at a trusted customer site with a restrictive security policy to intercept all HTTPs-Traffic using a customer-provided certificate which never fits to the visited web-sites.
Most of my technical research jobs using Google aren’t secret, otherwise I won’t pass them to Google, so HSTS for at least Google-Sites doesn’t makes sense in these cases.
Google knows that and invented the no-HSTS-Switch:
--ignore-certificate-errors
"C:\Program Files (x86)\Google\Chrome\Application\chrome.exe" --ignore-certificate-errors
Thank you!